“We’ll Just Hire Experts When Needed” but Expertise Is Not an On/Off Toggle
 You’ve probably heard this before, maybe even said it yourself: “We’ll just hire an expert when something breaks.”
You’ve probably heard this before, maybe even said it yourself: “We’ll just hire an expert when something breaks.”
It sounds reasonable enough. Why pay for ongoing IT support if you need help only every now and then, right?
But here’s the thing: Expertise doesn’t work like a light switch you can flick on when it suits you. When you treat IT as something you deal with only when there’s an emergency, you’re already on the back foot.
Let’s look at why that mindset quietly costs more than it saves.
The Hidden Cost of Reactive Expertise
When you call in an expert after something breaks, you’re not just paying for the fix; you’re paying for the downtime, the frustration, and the uncertainty that comes with not knowing how serious the problem really is.
An hour of IT downtime rarely means an hour of lost work. It can snowball into missed deadlines, irritated clients, and a team that can’t move forward.
And the expert you’ve called? They’re starting cold. They don’t know your systems, how they’re configured, or what’s been tried before. It’s like calling a plumber to fix a burst pipe in a house they’ve never seen. They’ll get it done, but not without wasting time even figuring out where the shut-off valve is.
The Trust Curve
Every outside expert starts at zero on the trust curve. They don’t know your setup, your people, or your tolerance for risk.
A managed service provider (MSP) takes the opposite approach. We build that trust over time. We learn what “normal” looks like in your environment, which allows us to spot problems before they turn into full-blown outages.
You can’t buy that kind of familiarity in a single call-out; it’s earned through consistent, ongoing involvement.
Reactive Experts vs. Embedded Experts
There’s a big difference between an expert you call in and one who’s already embedded in your operations.
Reactive experts fix problems; embedded experts prevent them.
A reactive expert drops in, tackles the surface issue, and moves on. There’s no pattern recognition, no system-wide improvement, and no strategy.
An embedded expert, such as an MSP, keeps a pulse on your systems constantly. We track performance, maintain updates, check backups, and plan ahead so your technology quietly supports your business goals. Instead of waiting for things to break, we make sure they don’t.
You Can’t Outsource Familiarity
Familiarity isn’t a technical skill; it’s earned by spending time inside your business.
You could hire the best IT consultant in the country, but if they don’t know your network layout, where your data lives, or how your team operates, they’re flying blind.
When you work with an MSP, we become part of your business. We learn the quirks of your setup, the tools your team relies on, and even who to call when something seems off. That level of understanding leads to faster fixes and smarter long-term decisions.
The Smarter Approach
Hiring experts only “when needed” might look efficient on paper, but it’s a false economy. A smarter approach is having proactive experts who already know your systems, quietly keeping everything steady in the background.
With an MSP partnership, you get a team that:
- Monitors your systems around the clock.
- Spots and fixes issues early.
- Keeps your software and security current.
- Plans upgrades before they become urgent.
- Aligns technology with your goals.
You still get expertise when you need it, but you also get predictability, consistency, and peace of mind the rest of the time.
The Takeaway
Expertise isn’t something you can just “turn on” when it’s convenient. It’s a relationship that builds over time, and the payoff grows the longer you invest in it.
If your business still runs on the “call for help when it breaks” model, it might be time to rethink. Partnering with a managed service provider gives you steady, proactive support that keeps everything running smoothly and saves you from costly surprises later.
Let’s talk about how we can make that happen for your business. Call us at 416) 645-2469, and let’s get you started with proactive support!
Want to be notified when our next blog is posted, sign up here.

 Most adults have learned to ignore sketchy pop-ups, closing the tab, reading the warning, and moving on. Kids, on the other hand, haven’t learned that instinct yet. When something flashes on the screen, they just want it to disappear so they can get back to YouTube or Roblox. That single click might seem harmless, but it can install unwanted software, change browser settings, and open the door for more pop-ups later.
Most adults have learned to ignore sketchy pop-ups, closing the tab, reading the warning, and moving on. Kids, on the other hand, haven’t learned that instinct yet. When something flashes on the screen, they just want it to disappear so they can get back to YouTube or Roblox. That single click might seem harmless, but it can install unwanted software, change browser settings, and open the door for more pop-ups later.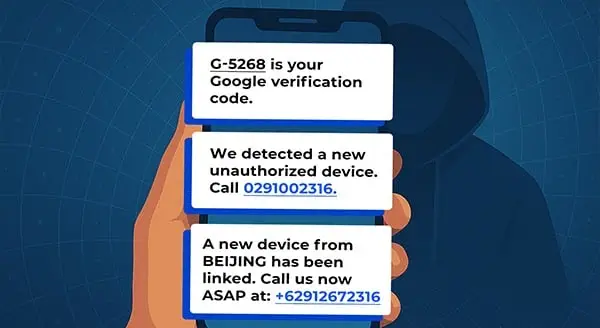
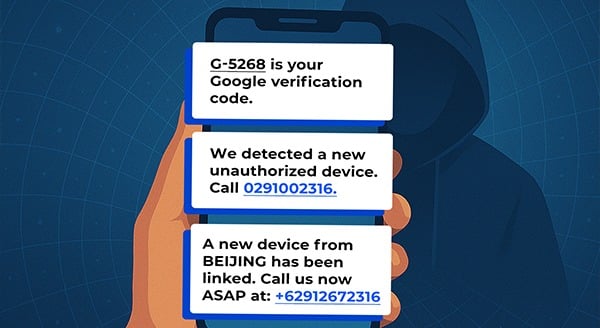 You’ve probably seen those text messages from Google with a code, the ones that pop up when you sign in from a new device or reset your password. They usually come from a sender called “Google,” and because it looks familiar, most of us don’t think twice when we see it.
You’ve probably seen those text messages from Google with a code, the ones that pop up when you sign in from a new device or reset your password. They usually come from a sender called “Google,” and because it looks familiar, most of us don’t think twice when we see it.
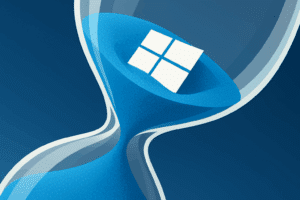 On October 14, 2025, Windows 10 stopped receiving security and reliability updates. Your PCs will still run, but new threats will no longer be patched. For a business, that means rising risk and tighter compliance scrutiny. Let’s look at your options and what makes sense in practical terms.
On October 14, 2025, Windows 10 stopped receiving security and reliability updates. Your PCs will still run, but new threats will no longer be patched. For a business, that means rising risk and tighter compliance scrutiny. Let’s look at your options and what makes sense in practical terms.
 If you run a business, the technology you choose matters more than you might think. It’s tempting to save money by picking up consumer-grade laptops, routers, and software, but this decision often backfires. What works fine for home users can cause major headaches in a business setting, leading to security risks, unexpected downtime, and higher costs in the long run.
If you run a business, the technology you choose matters more than you might think. It’s tempting to save money by picking up consumer-grade laptops, routers, and software, but this decision often backfires. What works fine for home users can cause major headaches in a business setting, leading to security risks, unexpected downtime, and higher costs in the long run. With Windows 10’s end of life scheduled for October 14, 2025, it may seem like there’s plenty of time to prepare. But if you wait too long, you could end up scrambling for a solution as the deadline approaches. Understanding what’s at stake and how to plan now can save your business from unexpected downtime, security issues, and potential workflow disruptions.
With Windows 10’s end of life scheduled for October 14, 2025, it may seem like there’s plenty of time to prepare. But if you wait too long, you could end up scrambling for a solution as the deadline approaches. Understanding what’s at stake and how to plan now can save your business from unexpected downtime, security issues, and potential workflow disruptions.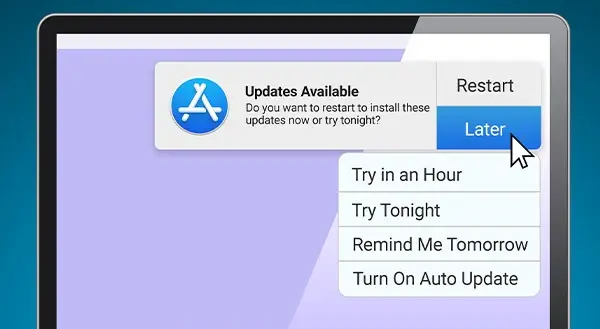
 We’ve all been there. You’re in the middle of something important when that pesky update notification pops up. “Now is not a good time,” you think, and click “Remind me later.” The problem is that “later” never seems to come. Weeks, months, even years go by, and your laptop is still running the same old version of its operating system.
We’ve all been there. You’re in the middle of something important when that pesky update notification pops up. “Now is not a good time,” you think, and click “Remind me later.” The problem is that “later” never seems to come. Weeks, months, even years go by, and your laptop is still running the same old version of its operating system.
 What Is World Backup Day?
What Is World Backup Day?
 Collaboration Tools Have Changed How We Work
Collaboration Tools Have Changed How We Work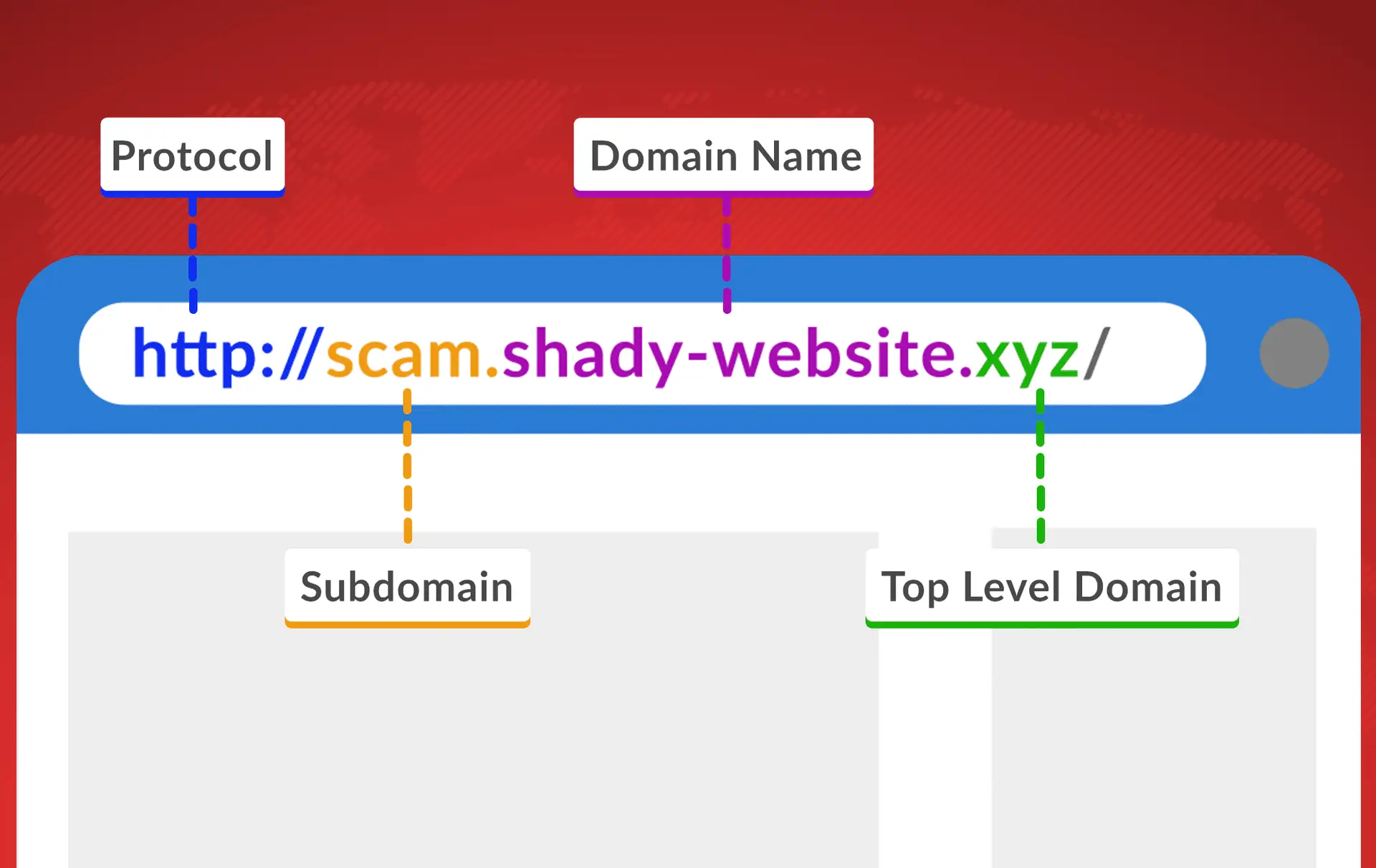
 Hackers Hide in the Hyperlinks: Spotting Malicious URLs
Hackers Hide in the Hyperlinks: Spotting Malicious URLs